System abuse is not a shortcut. It is a criminal offence.
What the Law Says
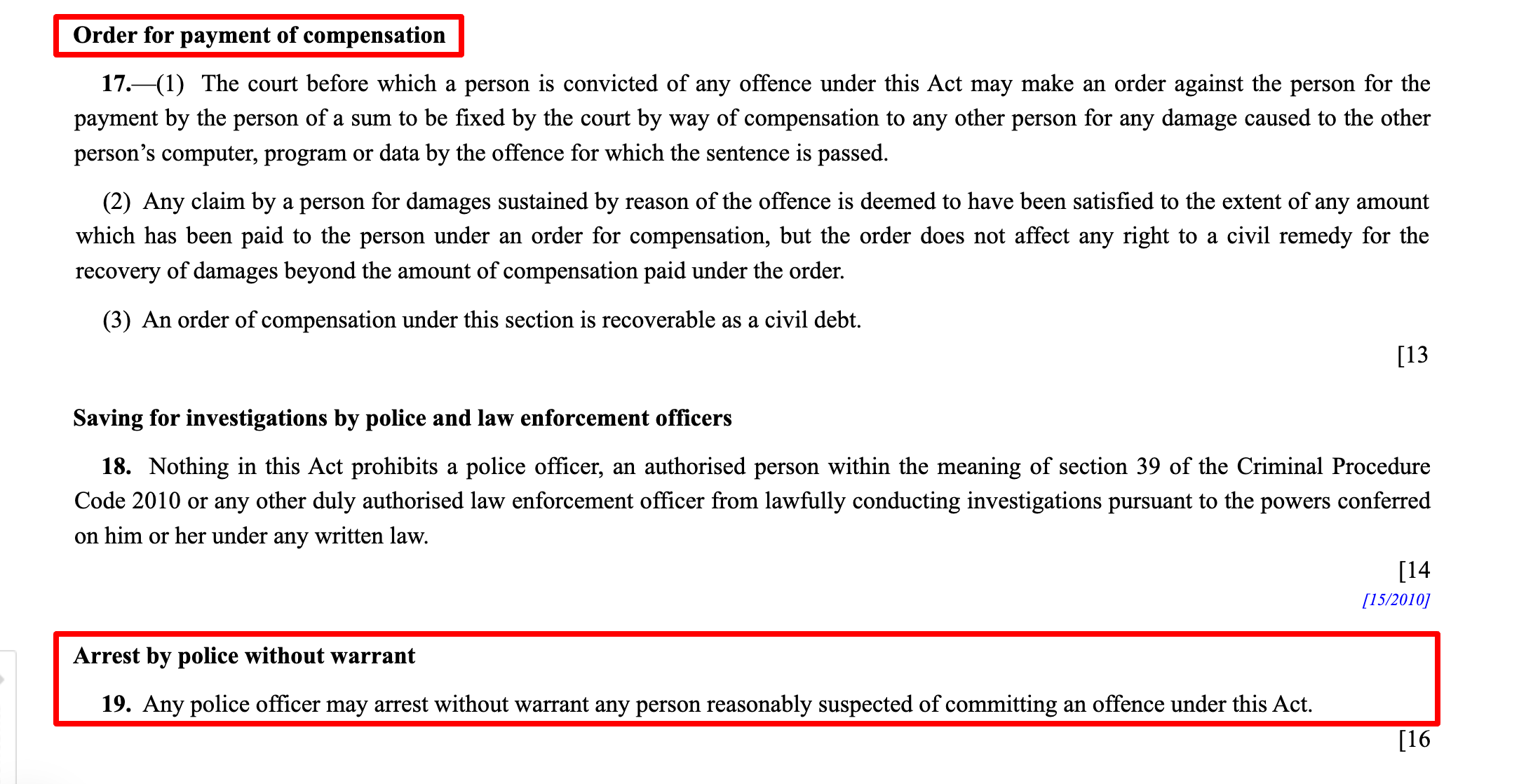
Under the Computer Misuse Act 1993:
It is illegal to:
- Access systems without authorization
- Modify data without permission
- Use systems for unintended purposes
- Disrupt or interfere with system operations
- Share or misuse access credentials
Even attempts or assisting others are punishable.
What This Means in Redbrick
- No accessing cases that are not yours
- No editing or overriding data without approval
- No using CRM data for personal gain
- No sharing logins or system access
- No bypassing system processes
If you are not authorised, you do not touch it.
Common Risk Scenarios
- Logging into someone else’s account
- Using shared credentials
- Editing records to “fix” a case
- Extracting client data for external use
- Trying to bypass system restrictions
Convenience is not a valid excuse.
Types of Offences
- Unauthorized access to computer material
- Unauthorized modification of data
- Unauthorized use of computer services
- Unauthorized obstruction of systems
- Unauthorized disclosure of access codes
- Access with intent to commit further offences
Consequences
- Criminal offence
- Immediate termination
- Loss of system access and career impact
The system logs everything. There is no hiding.